Table of Contents
Citrix NetScaler Exploited in Active Attacks. Citrix is widely used by businesses all over the world to handle remote access and secure application delivery. Due to their widespread use, they are frequently targeted by cybercriminals looking to take advantage of weaknesses. Recently, real-world attacks have actively exploited crucial weaknesses, posing a serious risk to organizations. Unauthorized access, data theft, and even widespread failures might result from these assaults. Staying safe starts with knowing why Citrix products are in the news.
Understanding the Exploited Vulnerability
CVE-2025-7775, the most recent Citrix NetScaler vulnerability, is a critical remote code execution (RCE) vulnerability. It means that malicious instructions can be executed on unpatched NetScaler systems by attackers without requiring valid login information. This vulnerability is being used by cybercriminals to install malware, obtain unauthorized access, and steal confidential information. The breaches, which target companies that have not yet implemented Citrix’s security patch, are confirmed to be operational in the wild. Security professionals categorize it as a high-risk vulnerability that has to be patched due to its severity.
Impact of Exploitation on Businesses
The Citrix NetScaler vulnerability can put companies at risk of major breaches of data and sensitive information theft if it is not fixed. Unauthorized access to internal systems could give attackers the ability to modify or steal data that is vital to the operation of the company. Such flaws are frequently used to initiate ransomware attacks, which result in system lockdowns. Long-term outages that interfere with operations and customer service may be the outcome. In addition to monetary losses, businesses also risk harm to their reputation and a decline in consumer confidence.
How to identify if you are affected
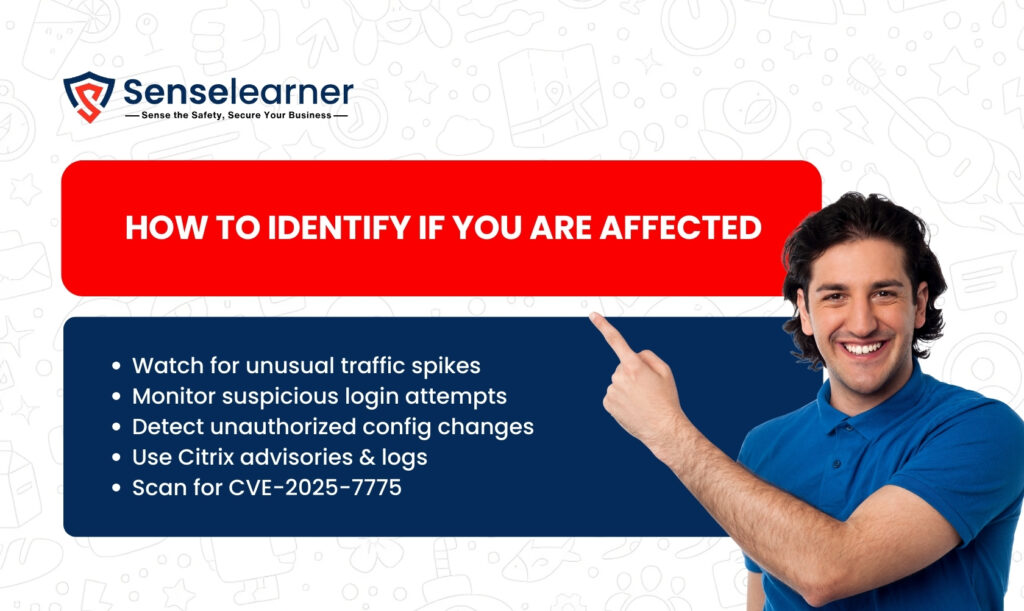
Unusual traffic patterns or sudden spikes in use of resources should be watched by organizations as these could be signs of exploitation. Be careful of shady login attempts, particularly when they come from unfamiliar IP addresses or at strange times. Unauthorized modifications to Citrix NetScaler configuration parameters are warning signs of compromise. To look for signs of an attack, security teams can use Citrix’s official advisories and tools in addition to log analysis. Verifying whether systems are vulnerable can be done by using vulnerability scanners or scripts that check for the CVE-2025-7775 exposure.
Visit Citrix patches three netscaler
Citrix official response and Security Patches
Citrix announced an official security patch to address the vulnerability after acknowledging that CVE-2025-7775 is being actively exploited. All supported versions of NetScaler ADC and Gateway can receive the upgrade, which comes with detailed deployment instructions. Since hackers are already searching the internet for unpatched systems, it is essential that this patch be applied right away. Organizations that put off updates run the risk of ransomware, data breaches, and service disruptions. Businesses can seal the security flaw before it can be further abused by applying timely patches.
How to stay protected: Best Security Practices
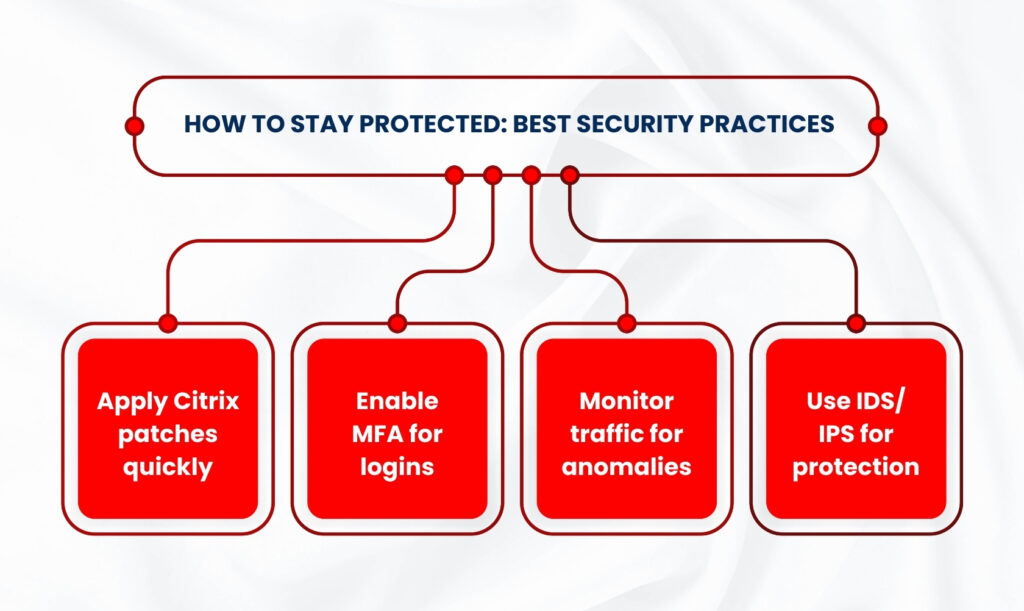
When Citrix releases security fixes, the first and most crucial thing to do is to apply them. Companies should also use network segmentation to prevent attackers from moving freely across systems, even if they manage to get access. Activating multi-factor authentication (MFA) provides an additional degree of security against unwanted login attempts. Before significant damage happens, unusual patterns can be found with the aid of ongoing traffic monitoring. Lastly, the implementation of intrusion detection and prevention systems (IDS/IPS) strengthens defenses against current and potential assaults.
Steps for incident response if already compromised

Isolating the infected system from the network is the first step to prevent the spread of the corrupted Citrix NetScaler. To find out how the attackers obtained access and what information might have been compromised, do a forensic study thereafter. Apply Citrix’s security patch or workaround as soon as you understand the problem to eliminate the vulnerability. Resetting all credentials, including admin and user accounts, is also necessary to stop access from being reused. Last but not least, keep a careful eye on logs and traffic to make sure the attackers haven’t left any backdoors or enduring dangers.
Also read French Retailer Auchan hit by cyberattack
Long term cybersecurity strategies for enterprise
In order to find and fix security vulnerabilities before attackers take advantage of them, businesses should implement routine vulnerability management. Using realistic attack simulations, periodic penetration testing assists in identifying vulnerabilities in networks and systems. Staff members are guaranteed to be able to identify phishing attempts and follow safe procedures through ongoing cybersecurity training. Verifying each user and device before allowing access lowers risks even more when a zero-trust security model is used. A more effective and proactive protection against changing cyberthreats is created when these tactics are combined.
Conclusion
A clear reminder that proactive defense is always preferable to damage control is the Citrix NetScaler exploitation. Businesses that neglect monitoring or postpone updates expose themselves to potential threats. Reducing exposure to significant vulnerabilities is best achieved by timely patching and ongoing monitoring. Businesses must view cybersecurity as a continuous priority rather than a one-time activity, even beyond technical fixes. Businesses are able to improve their security and remain ahead of the curve by learning from this attack.